Happy Holidays everyone! Tis the time to be relaxing with family or just sitting in your office writing a blog. 🙂 This post is brought to you thanks to a FOR585 Advanced Smartphone Forensic alumni who could not locate an artifact he learned about in class. This artifact is tied to Apple Maps on iOS devices. The file of interest is the GeoHistory.mapsdata, which was introduced with iOS 8 and has been tracking the Apple Maps data since. This file replaced the legacy history.mapsdata file. This file was required for examination in his case. When he couldn’t find it, he reached out and sent me on a frenzy of testing. Since his question arrived in my inbox, I have been obsessed with figuring out what the “Grinch” did with it.
What I tested (thank you to my brave family and friends for letting me dump your phones for this research):
*Note: Some of the devices below are syncing with iCloud and some are not. I wanted to be thorough and make sure that the Grinch didn’t take the file to the cloud…
- iPhone 6s with a fresh install of 10.0.2
- iPhone 7 updated from previous iOS versions running 10.0.2
- iPhone 6s updated from previous iOS versions running 10.0.2
- iPhone 7 updated from previous iOS versions running 10.2
- iPhone 6s with a fresh install of 9.3 – jailbroken
- iPhone 6s+ with a fresh install of 10.1.1
- iPhone 6 updated from previous iOS versions running 10.1.1
- iPhone 6s+ updated from previous iOS versions running 10.2
- iPhone 7 updated from previous iOS versions running 10.1.1
For each of these devices, I opened Apple Maps and searched for items I could easily identify:
- Radio City Music Hall, NYC
- Malvern Buttery
Additionally, I sent my mother in law to the grocery store and had her literally use Apple Maps on her iPhone 6 running 10.1.1 to ensure the data would “stick.”
Once all data was populated, I conducted both iTunes backups, Cellebrite Physical Analyzer File System dumps (Methods 1 and 2 for non-jailbroken devices, Method 3 for jailbroken devices, and Method 1 for devices running 10.2) and BlackLight for acquisition of the data. I tried parsing the data dumps in BlackLight, Oxygen Detective, Magnet IEF, Cellebrite Physical Analyzer and manual examination to ensure I wasn’t overlooking something. I pulled my own cloud data with Elcomsoft and searched for the file in those backups with some luck – wait for that at the end.
When I manually examined the file system of the backups, I started to see major inconsistencies. The GeoHistory.mapsdata file was sometimes present and sometimes not. The history.mapsdata file was there no matter what. Based upon my experience with iOS device forensics, it seems that when Apple no longer uses a file, the file persists and is no longer updated. When Apple wants to protect a file, they encrypt it and/or make it inaccessible without a full physical image, which is currently not possible on new devices without a jailbreak.
Below is a list of the phones from above showing which devices presented access to the GeoHistory.mapsdata file. (Note: Additional testing was done by Sarah Edwards and Lee Crognale on their devices to confirm my findings – thanks a ton ladies.)
- iPhone 6s with a fresh install of 10.0.2 – GeoHistory.mapsdata was present and contained Apple Maps data
- iPhone 7 updated from previous iOS versions running 10.0.2 – NO GeoHistory.mapsdata
- iPhone 6s updated from previous iOS versions running 10.0.2 – GeoHistory.mapsdata was present and contained Apple Maps data
- iPhone 7 updated from previous iOS versions running 10.2 – NO GeoHistory.mapsdata
- iPhone 6s with a fresh install of 9.3 – jailbroken – GeoHistory.mapsdata was present and contained Apple Maps data
- iPhone 6s+ with a fresh install of 10.1.1 – NO GeoHistory.mapsdata
- iPhone 6 updated from previous iOS versions running 10.1.1 – NO GeoHistory.mapsdata
- iPhone 6s+ updated from previous iOS versions running 10.2 – NO GeoHistory.mapsdata
- iPhone 7 updated from previous iOS versions running 10.1.1 – NO GeoHistory.mapsdata
Here are some examples of what I was expecting to see:
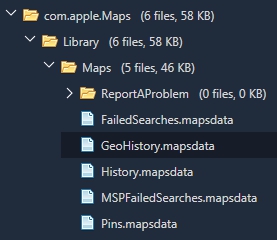
Example 1: An iPhone that has been updated to iOS 10+. We know it has been updated because we see the historical History.mapsdata file as well as the GeoHistory.mapsdata.
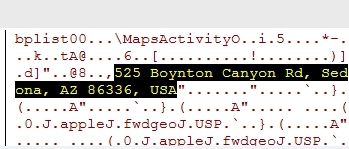
Example 2: Examining the Hex of the GeoHistory.mapsdata. Below we can see my search for Malvern Buttery.

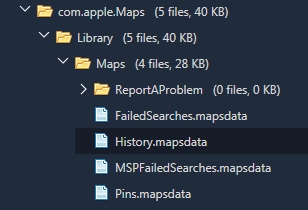
Example 3: What the data may look like – NOT GOOD! While the file, History.mapsdata, contains legacy searches in Apple Maps, it does not contain any data since iOS 8.
Continuous searching for locations that I populated in Apple Maps lead to two files that seemed to store the most recent search conducted and manual location entry in Apple Maps, but lacked additional artifacts. The first is /mobile/Applications/group.com.apple.Maps/Library/Preferences/group.com.apple.Maps.plist. In the example below, I used Apple Maps to search for a location in Sedona, AZ. Keep in mind that this was the most recent Apple Maps search on the device at that point in time ( I was running iOS 10.1.1). Nothing I searched for after that was found in this file.
The second location was mobile/Applications/com.apple.Maps/Library/Preferences/com.apple.Maps.plist. This was the only location where I could find my search for Radio City Music Hall. There was nothing of interest other than the fact that the location was listed with a bunch of yelp reviews.
My current location was not captured, which normally occurs in the .mapsdata files. I think this plist is tracking the last search within Apple Maps where the goup.com.apple.Maps.plist seemed to save the last manual entry in Apple Maps. Again, this is an assumption which requires further testing and research.
From the device side, it seems that the Grinch has stolen the GeoHistory.mapsdata from the following devices/versions:
- The iPhone 7 running any version starting with 10.0.2 – EVEN devices that have been updated from previous iOS versions.
- Any iPhone running iOS 10.1.1
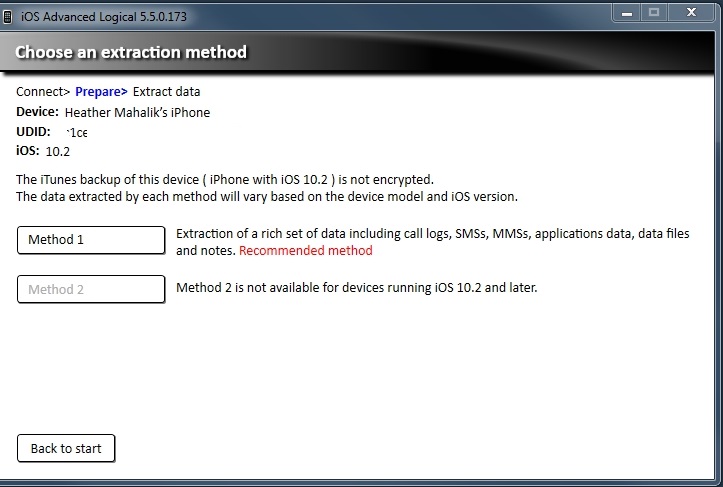
- WARNING: iOS 10.2 presents us with major hurdles and potentially missing artifacts that span beyond the GeoHistory.mapsdata. Get ready to learn ways around this… check out how it looks in Physical Analyzer below.
From the iCloud perspective. I used Elcomsoft Phone Breaker to extract my iCloud data. I had three snapshots in the cloud from two different iOS versions. (Keep in mind you need legal authority, consent or some form of permission to access cloud data.) What I found is even more confusing.
- iPhone 7 backup from iOS 10.2 – GeoHistory.mapsdata was present but not updated with current Apple Maps data
- iPhone 7 backup from iOS 10.1.1 – No GeoHistory.mapsdata
Not sure why the file is not present with 10.1.1 or where the Grinch put it, but I promise to keep searching. I plan to focus research on iOS 10.2, cloud data and additional location artifacts for the FOR585 course update and will blog on findings. I may even do a SANS webcast after the baby and I get settled in (yes, I am due to have a baby in 24 days.)
In the meantime, please test on your own devices and let me know if you find where the Grinch placed this file, if that is even possible. Also, make sure you always validate your findings and your tools. I know I taught my student the right way because he was manually digging to find the truth. That’s what mobile forensics is all about even when the results are not what we expect and the artifacts we need are stolen by the mean Grinch!
I’m really hoping that 2017 brings us a new artifact that is storing this data or we find a way to access this missing file. Happy Holidays!

Thanks for posting. Always interesting to read your articles. Good luck with your new addition.
Thank you !
Thank you for taking the time and putting this together Ma’am. I always learn a lot from your materials and I hope to take your class someday in the future.
Great Post Heather! Congratulations on your new baby! And Happy New Year!
Just an FYI – you can get a file system dump using the UFED4PC (didn’t try on the touches) on iOS 10.2. I had to test something with an iPhone 6 and that’s when I noticed that method 2 was greyed out, but I was able to capture more data using the UFED4PC over Physical Analyzer (go figure).